Want a tip? Have a tip. Sometimes tech, sometimes life, sometimes not a tip at all. Now faced with the prospect of not posting this month (shock and horror!), I throw ’em out there with wild abandon.
Satisfy* your hunger after the jump.
Most recently applicable to me: PsTools. If you know what that means, well, great. Hang around for the waffle, or something. To those of you not already in the know, PsTools is a collection of Windows troubleshooting and management utilities, within the larger Sysinternals suite of utilities. The utilities under the PsTools collection are aimed toward remote management of a Windows system, providing relatively easy methods of remotely executing commands on those systems. If you administrate Windows systems, there will come a time when the PsTools utilities prove themselves invaluable and you owe it to yourself to keep them in your proverbial toolbox.
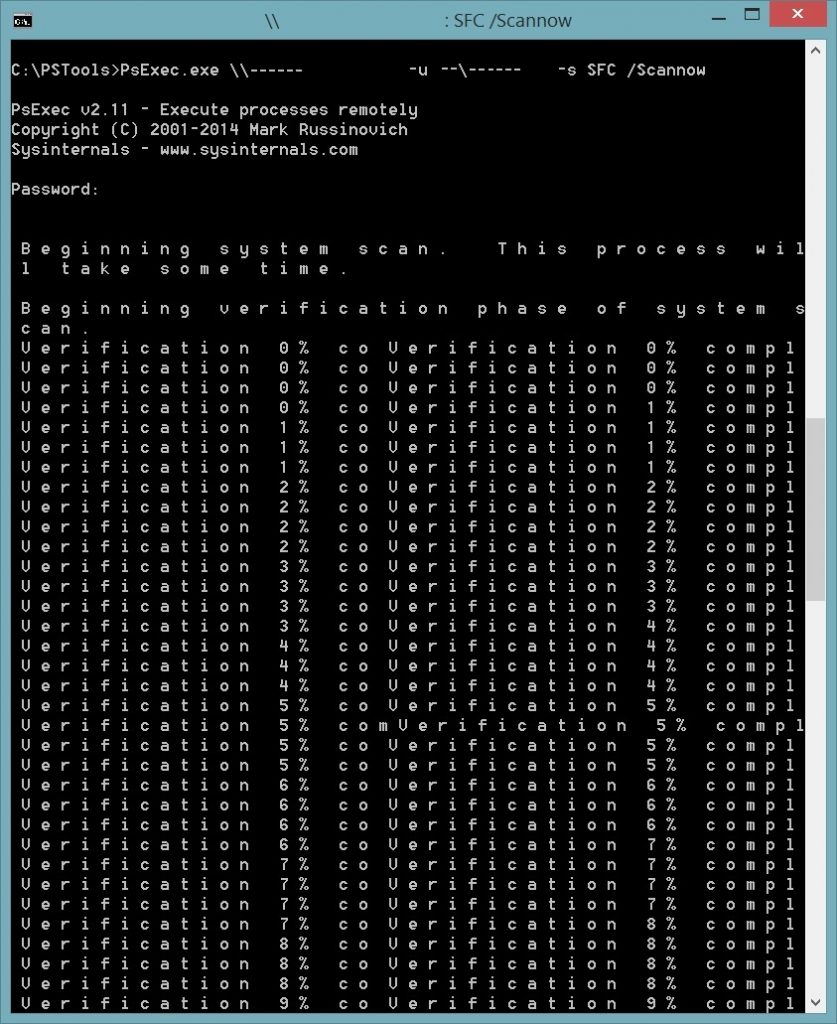
Today I used PsExec, a PsTools utility, to execute a Windows OS integrity scan on a system that had been powered off while updating and subsequently displayed only a mouse cursor when it started up. The command for that was:
> psexec \\hostname-or-ip -u domain\username -s sfc /scannowJust, y’know, use your remote system’s hostname or IP address as needed, and supply your own, administrative, domain and username combo (you’ll be asked for that account’s password on execution).
So many credits (probably all of them) to Mark Russinovich and the Winternals team, which Mark cofounded, who put the original Sysinternals tools together way back in 1996. Since then, the tools growing in use and function, Microsoft acquired Winternals and their software, along with bringing Mark (and probably others) on to continue their development (he’s CTO of Microsoft Azure now). Today the Sysinternals suite remains an indispensable asset of a Windows admin’s toolset, and rather than ineffectually attempt to scratch the surface of their usefulness, I’d encourage you to check out the Windows Sysinternals site and browse the troves of info and documentation there.
*YOUR HUNGER FOR KNOWLEDGE, THAT IS. HA. HA. HA.
Okay, truth be told, the Windows file validation thing didn’t work for the particular problem I was having – things were well broken (graphics driver corruption or something to that effect) and frankly it was quicker to swop the machine out and re-image it. That said, I think the use of PsTools and the know-how to run processes on a system remotely remain valuable skills so I’m going ahead with this post anyway.

![Like this, except [more || less] delicious.](https://r4mzy.co.za/wp-content/uploads/2016/05/00-tip-o-thursday.jpg)