So. You already know what’s happening here (probably) because the title is obvious (hopefully). But for the title-skippers in the crowd I’ll lay out the introduction-with-waffle: far too often I find myself having a go at a duck, in an effort to educate myself (again) about good partitioning schemes for new Linux installations (in this case Debian).

Is this a deep dive yet?
I’m tired of doing that, so now we have this post to document my latest preferred partition scheme. Now, when (not if) I’m repeating this Linux/Debian installation exercise in the future, I’ll just have a go at myself.
First of all, along my sometimes-repetitive travels I once came across the very handy CIS OS hardening and security benchmarks, on which I am basing the majority of this partition scheme. I even talked about it once before, and the Server Fault question I mention there was instrumental in guiding this scheme, too.
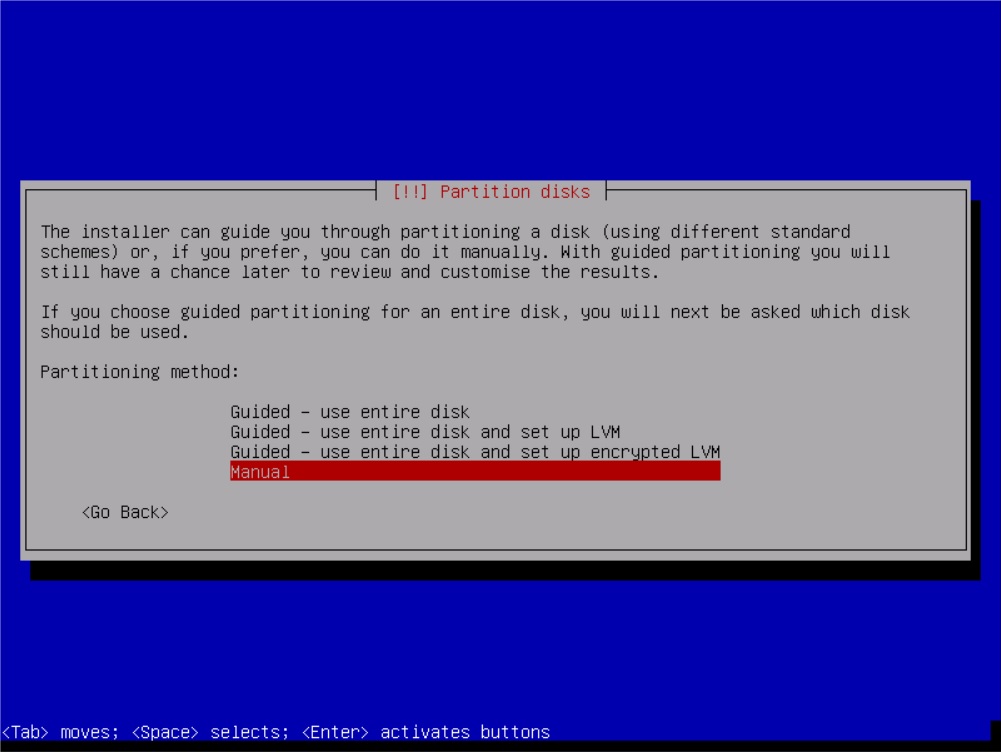
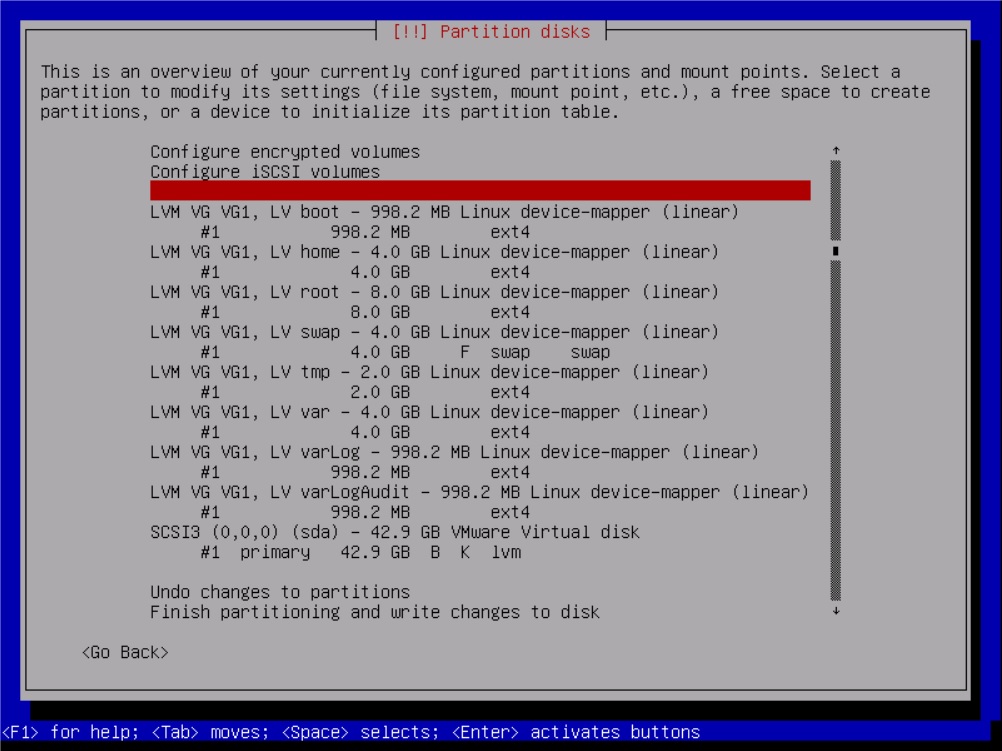
On with the details, then! So I’m rolling a fresh Debian Jessie virtual machine, and I’m implementing LVM (Logical Volume Manager) for easy partition management later on (in terms of future resizing and such; I’m not sure what, if any, performance impact there is between LVM and “normal” partitions but my reading indicates it’d be negligible). Not being terribly familiar with LVM, this presented a minor learning curve insofar as figuring out just how to set up a volume group and logical volumes (logical volumes are effectively the “partitions” to a regular, non-LVM setup – one for each mount point – while volume groups could be called a “parent” of the logical volumes). Then came actually setting the mount points on each of those logical volumes. Some 20 minutes of actual, undistracted focus got me through it, and, without further ado, my volume and mount-point structure, on installation, goes like so:
/ 8000MB default /boot 1000MB nodev /home 4000MB nodev /tmp 2000MB noexec, nodev, nosuid /var 4000MB default /var/log 1000MB default /var/log/audit 1000MB default swap varies n/a
Having set out my partition scheme, I picked my installation options and forged ahead with installation.
With the OS core installed and my partition scheme quest just about ready to hand in, I decided to go just a bit further with a quick side-quest, and set out some recommended directory mounts and restrictions. That is, I edited my FSTAB (/etc/fstab) to bind /var/tmp to the /tmp partition and to restrict the /run/shm directory. To do that, I added these lines to my FSTAB file:
/tmp /var/tmp none bind 0 0 none /run/shm tmpfs nodev,nosuid,noexec 0 0 none /dev/shm tmpfs nodev,nosuid,noexec 0 0
Admittedly, I don’t fully understand the relationship between /run/shm and /dev/shm – the latter now points to the former but the CIS benchmark only mentions the former so I decided to do both. There’s more about what’s going on between those two, and their relationship in newer versions of Debian, here.
I didn’t do anything with the removable device recommendations in the CIS benchmark – being a VM, this machine is unlikely to ever see any removable devices. I’m more likely to just disable the option to mount them to the machine at all and be done with it. I am curious as to whether there’s a way to “dynamically” restrict /all/ future-inserted removable devices in such a fashion, though… I also went ahead with implementing the benchmark’s recommendations for disabling the mounting of their listed file systems, and disabled auto-mounting.
“auto mount”
Lastly, at this point anyway, we have the Secure Boot Settings. I made the user and group ownership and permissions changes as described in the benchmarks. Next up was the boot loader password – whoo boy… But I’ve already talked about that adventure. And as for anything beyond that? Well, the scope here was just the partition scheme and I’ve already broken that. You have the benchmarks available to you – go check ’em out.
Happy hardening! ;)